What is Infrastructure as Code? - Definition & Meaning
Infrastructure as Code defines servers and networks in Terraform or Pulumi, yielding reproducible, version-controlled environments instead of manual setup.
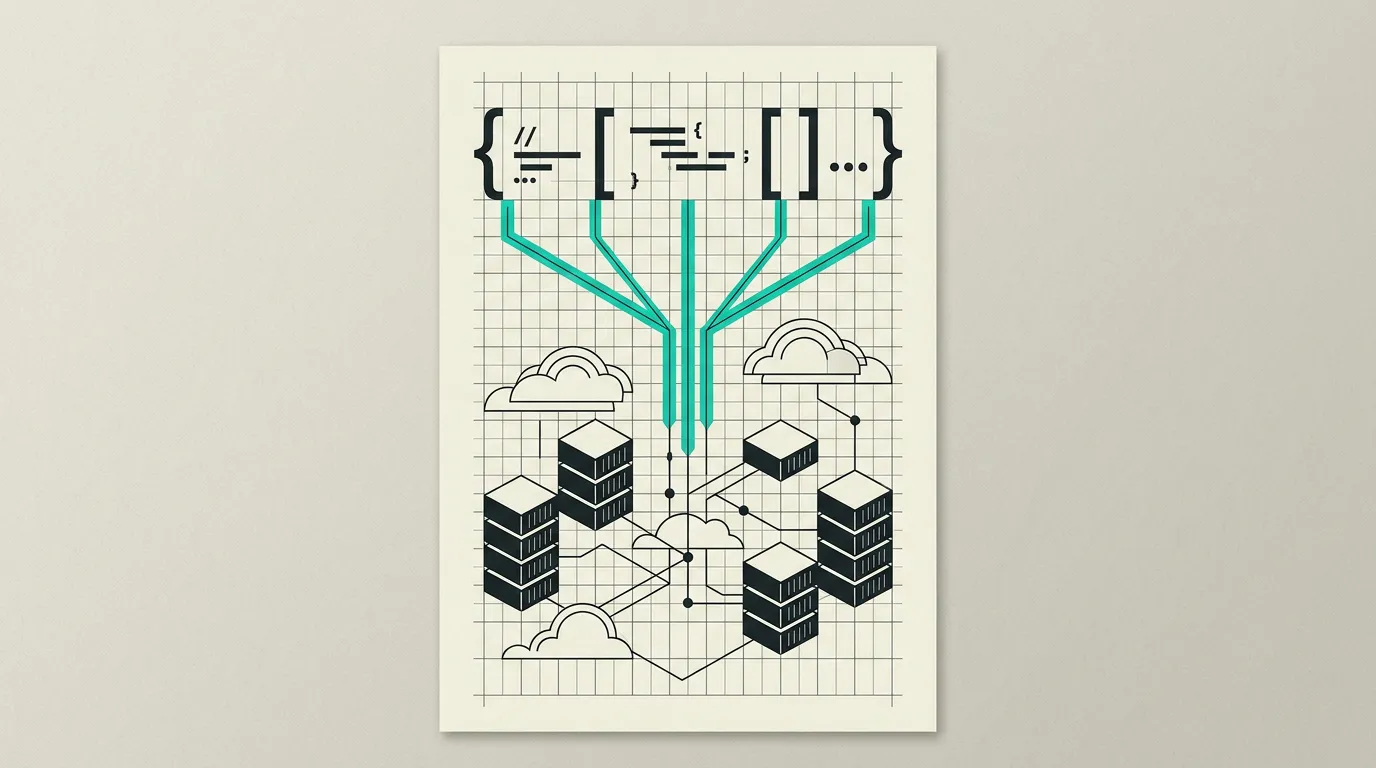
Infrastructure as Code (IaC) is the practice of managing and provisioning IT infrastructure through machine-readable configuration files rather than manual processes. Servers, networks, databases, and load balancers are described as code stored in version control, reviewed via pull requests, and applied automatically. This makes infrastructure reproducible, version-controlled, testable, and automatable, with the same discipline that applies to application code. IaC is a foundational pillar of modern DevOps practices and enables continuous delivery of infrastructure changes.
What is Infrastructure as Code?
Infrastructure as Code (IaC) is the practice of managing and provisioning IT infrastructure through machine-readable configuration files rather than manual processes. Servers, networks, databases, and load balancers are described as code stored in version control, reviewed via pull requests, and applied automatically. This makes infrastructure reproducible, version-controlled, testable, and automatable, with the same discipline that applies to application code. IaC is a foundational pillar of modern DevOps practices and enables continuous delivery of infrastructure changes.
How does Infrastructure as Code work technically?
IaC tools follow two approaches: declarative (you describe the desired end state and the tool calculates what changes are needed) and imperative (you describe the steps to reach that state). Terraform by HashiCorp is the market leader with HCL (HashiCorp Configuration Language) for declarative infrastructure definitions and supports hundreds of providers for AWS, Azure, GCP, Cloudflare, Vercel, and more. Terraform manages state in a state file that tracks current infrastructure state and calculates an execution plan via terraform plan, showing exactly which resources will be created, modified, or destroyed. State locking via DynamoDB or similar backends prevents two engineers from applying changes simultaneously. Pulumi differentiates by using standard programming languages (TypeScript, Python, Go, C#) instead of a DSL, simplifying conditional logic, loops, abstractions, and unit testing. AWS CloudFormation is the native IaC tool for AWS with JSON/YAML templates and deep integration with AWS services. GitOps combines IaC with Git as the single source of truth: infrastructure changes are reviewed via pull requests and automatically applied by reconciliation tools like ArgoCD or Flux. Modules and stacks promote reuse: common patterns (VPC, database cluster, monitoring stack) are defined once and deployed multiple times with different parameters. Drift detection signals when actual infrastructure diverges from the desired state, for example after manual changes in the cloud console. Policy-as-code tools like Open Policy Agent (OPA) and Sentinel enforce compliance rules before changes are applied. Terragrunt simplifies managing multiple Terraform configurations by applying DRY principles to backend configuration, provider settings, and module parameters, reducing boilerplate across environments. AWS CDK (Cloud Development Kit) offers an alternative where infrastructure is defined in TypeScript, Python, or Java and synthesized into CloudFormation templates. Infracost integrates with CI pipelines to forecast the cost impact of infrastructure changes before they are applied, so teams make cost-aware decisions. Limiting blast radius is a key design principle: small, focused stacks with clear boundaries prevent a single mistake from damaging the entire infrastructure. Terraform workspaces enable managing multiple instances of an environment with the same code, for example per customer or per region.
How does MG Software apply Infrastructure as Code in practice?
At MG Software, we manage all cloud infrastructure through code. We use Terraform for provisioning databases, networks, DNS records, and Kubernetes clusters, with state stored in a remote backend with encryption and locking. All infrastructure changes go through code review via pull requests and are automatically rolled out via our CI/CD pipeline, with terraform plan posted as a comment on the PR so reviewers see exactly what will change. We use modules for reusable components shared across client projects, such as standard VPC configurations and monitoring stacks. Infracost reports expected monthly cost changes directly in the pull request so cost overruns are caught early. We run periodic drift detection in CI to automatically flag manual console changes and alert the team before configurations diverge from the declared state. This guarantees that client environments are consistent, reproducible, and auditable.
Why does Infrastructure as Code matter?
Manually configured infrastructure is non-repeatable, error-prone, and unauditable. When the only person who set up the server leaves, knowledge about the configuration vanishes. IaC solves this by treating infrastructure as code: versionable, reviewable, testable, and reproducible. During incidents, the full production environment can be rebuilt from code within minutes rather than days of manual work. Teams that consistently apply IaC report up to 70% fewer configuration-related incidents. Auditors value the complete traceability through Git history, which significantly accelerates compliance processes such as SOC 2 and ISO 27001. For businesses, this means faster provisioning (minutes instead of days), reliable disaster recovery (rebuild infrastructure from Git), and compliance via audit trails that show exactly who changed what and when.
Common mistakes with Infrastructure as Code
Terraform state lives on laptops, gets corrupted, or leaks secrets like database passwords. Engineers click-change resources in the cloud console and are then surprised by the drift that terraform plan shows. Modules are never reused and every environment is a diverging fork with subtle configuration differences. CI runs terraform apply without a human reviewing the plan. IaC code is treated as throwaway scripts without unit tests, rollback strategy, or clear ownership per stack. Blast radius is ignored: a single state file contains all resources, so a mistaken terraform destroy deletes the entire production environment. Sensitive outputs are logged in CI without masking, exposing secrets in build logs for anyone with repository access.
What are some examples of Infrastructure as Code?
- A startup using Terraform to provision a complete AWS environment in a single command: VPC with public and private subnets, RDS PostgreSQL database with automated backups and multi-AZ failover, ECS cluster for containerized workloads, and an Application Load Balancer with SSL termination, all reproducible from a single codebase.
- A DevOps team using Pulumi with TypeScript to conditionally define staging and production environments within the same codebase, with environment-specific parameters passed via stack configuration files and unit tests verifying that production always has encryption and multi-AZ enabled.
- An enterprise implementing GitOps where all infrastructure changes are reviewed via pull requests, tested by a plan preview in CI, and ArgoCD automatically enforces the desired state on the Kubernetes cluster with automatic rollback on failures.
- A SaaS company reusing Terraform modules to provision an isolated environment for each new customer with their own database, Redis instance, and CDN configuration, all from the same modular codebase.
- A fintech organization integrating Open Policy Agent with Terraform to enforce compliance rules before changes are applied: no publicly accessible S3 buckets, mandatory encryption on all databases, required tagging for cost allocation, and automatic blocking of resources that do not meet the security standards.
Related terms
Frequently asked questions
We work with this every day
The same expertise you are reading about, we put to work for clients across Europe.
See what we doRelated articles
What Is DevOps? Practices, Tools, and Culture for Faster Software Delivery
DevOps unifies development and operations teams through automation, shared ownership, CI/CD pipelines, and Infrastructure as Code. Learn how DevOps practices enable reliable, frequent software releases and faster time to market.
What Is CI/CD? Continuous Integration and Delivery Pipelines for Reliable Software Releases
CI/CD automates the entire process of building, testing, and deploying code so development teams ship to production reliably, multiple times per day. Learn how pipelines work, which tools to choose, and what CI/CD delivers for your organization.
What is Docker? Complete Guide to Containerization for Development Teams
Docker packages applications with all dependencies into lightweight containers that run identically on any machine. Discover how containerization accelerates your development workflow, makes deployments reliable, and eliminates environment inconsistencies.
Qwik Alternatives That Ship Production Apps Today
Resumability is promising but the ecosystem is small. Five frameworks that already deliver what Qwik promises for your next production project.