What is an API Gateway? - Definition & Meaning
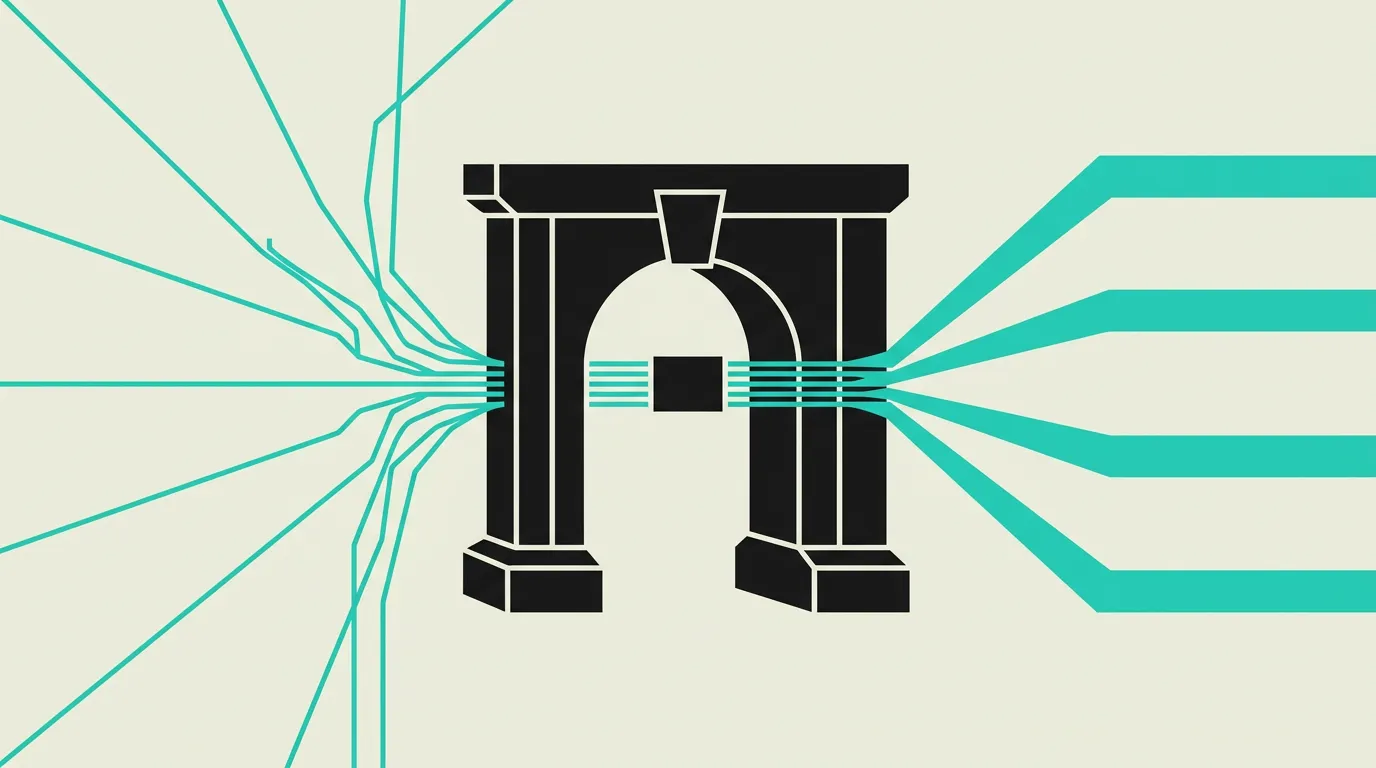
An API Gateway serves as the front door to your microservices: routing, rate limiting, authentication, and monitoring from a single entry point.
An API Gateway is a management layer that serves as the central entry point for all API requests in a distributed system. It routes requests to the appropriate backend services and provides functionality such as authentication, authorization, rate limiting, request transformation, and monitoring. By centralizing these cross-cutting concerns, individual services no longer need to implement security and traffic logic themselves.
What is API Gateway?
An API Gateway is a management layer that serves as the central entry point for all API requests in a distributed system. It routes requests to the appropriate backend services and provides functionality such as authentication, authorization, rate limiting, request transformation, and monitoring. By centralizing these cross-cutting concerns, individual services no longer need to implement security and traffic logic themselves.
How does API Gateway work technically?
An API Gateway sits between clients and backend services, handling cross-cutting concerns before requests reach business logic. Core capabilities include request routing (forwarding requests to the correct microservice based on URL path, headers, or payload), authentication and authorization (JWT validation, OAuth 2.0 flows, API key verification, and scope-based access control), rate limiting (restricting requests per client, IP, or time unit to prevent abuse and overload), and request/response transformation (adding headers, restructuring payloads, protocol conversion). Kong is a popular open-source gateway built on NGINX with an extensive plugin ecosystem for logging, CORS, IP restrictions, and custom middleware. AWS API Gateway offers serverless integration with Lambda functions and automatic scaling. Traefik integrates seamlessly with container orchestration like Kubernetes and auto-discovers services via labels. API versioning via the gateway enables serving multiple API versions simultaneously so older clients do not break when updates ship. Circuit breakers detect when a backend service fails repeatedly and temporarily return a fallback response, preventing cascading failures. Gateway-level caching reduces load on downstream services for frequently accessed, rarely changing endpoints. Logging and distributed tracing (OpenTelemetry) at the gateway provide comprehensive observability across all incoming requests. gRPC-to-REST transcoding enables exposing internal gRPC services via REST endpoints for web and mobile clients that lack protobuf tooling. Request aggregation, also known as Backend-for-Frontend (BFF), allows the gateway to combine responses from multiple backend services into a single response for the client, reducing the number of roundtrips and simplifying client-side logic. Canary releases and blue-green deployments are facilitated by the gateway splitting traffic percentage-wise across different backend versions, enabling gradual rollouts with instant rollback capabilities. WebSocket proxying through the gateway requires special handling for connection upgrades and long-lived connections; gateways like Kong and Traefik support this via dedicated plugins or middleware. Mutual TLS (mTLS) at the gateway verifies not only the client identity but also the backend service identity, adding an extra security layer in zero-trust architectures where no network traffic is implicitly trusted. OpenAPI schema validation on the gateway rejects malformed requests before they reach backend services, reducing unnecessary load and preventing unexpected input from causing errors downstream.
How does MG Software apply API Gateway in practice?
At MG Software, we implement API Gateways in projects with multiple backend services or when a public API needs to be secured and managed. We configure rate limiting per client and per endpoint to prevent API abuse, JWT authentication with scope-based authorization for secured endpoints, CORS policies for browser clients, and structured request logging for debugging and monitoring. For Kubernetes deployments, we use Traefik as Ingress with built-in gateway functionality and automatic service discovery via pod labels. For serverless architectures, we deploy AWS API Gateway with Lambda integration and usage plans for tiered access control. We also use OpenAPI specifications to automatically configure schema validation on the gateway, ensuring malformed requests are rejected before they burden backend services. For projects with external API consumers, we generate interactive API documentation from the same OpenAPI specs, which accelerates partner onboarding and reduces the number of support tickets. This provides our clients with a secure, well-managed, and scalable API layer that grows with their business.
Why does API Gateway matter?
Without an API Gateway, clients must know all internal services and call them directly, leading to tight coupling, duplication of security logic across services, and a larger attack surface. A gateway centralizes authentication, rate limiting, and observability in one place, drastically simplifying security and operational management. For businesses, this means faster onboarding of API consumers, better protection against abuse, and a consistent audit trail for compliance purposes. For companies that offer their API as a product, the gateway makes it possible to implement usage-based billing by accurately counting requests per customer. The investment in a gateway pays for itself quickly through reduced risk of security incidents and the operational hours saved by not reimplementing cross-cutting concerns in every individual service.
Common mistakes with API Gateway
The gateway accumulates domain logic that belongs in services, making gateway deployments risky. Rate limits are missing so a single misbehaving client can starve all downstream services. TLS terminates at the edge but east-west traffic stays plaintext on a flat network, making internal traffic interceptable. Teams expect a gateway to automatically replace a service mesh without configuring distributed tracing, circuit breakers, or schema validation. Logging captures only HTTP status codes without request body or latency breakdown. API versioning is not implemented, so a breaking change in a backend simultaneously breaks every consuming client. Gateway timeout configuration is set too generously, causing a slow backend to exhaust the gateway connection pool and render all routes unreachable.
What are some examples of API Gateway?
- A fintech platform using Kong API Gateway to route payment API requests to the correct processing service, with rate limiting of 100 requests per minute per client, automatic circuit breaking on downstream failures, and detailed audit logging of every financial transaction for compliance purposes.
- A mobile app backend using AWS API Gateway to authenticate incoming requests with JWT tokens, check authorization based on scopes, and forward requests to various Lambda functions without the app needing to know individual service URLs, while usage plans enforce different rate limits for free and premium tiers.
- An e-commerce platform implementing API versioning through the gateway so v1 and v2 clients are served simultaneously, with automatic request transformation converting old payloads to the new format and canary routing that gradually shifts traffic from v1 to v2 during the migration period.
- A healthcare API using a gateway for HIPAA-compliant logging of all requests, including request/response sanitization that masks sensitive patient data in log files, mutual TLS authentication between the gateway and backend services, and IP allowlisting restricted to authorized hospital networks.
- A multi-tenant SaaS platform configuring different rate limits and feature flags per tenant on the API Gateway, so free-tier and enterprise customers use the same endpoints but with different throughput limits, response enrichment, and access to premium-only endpoints controlled entirely at the gateway layer.
Related terms
Frequently asked questions
We work with this every day
The same expertise you are reading about, we put to work for clients across Europe.
See what we doRelated articles
What is DDoS Protection? - Explanation & Meaning
DDoS protection defends applications against massive traffic floods that overwhelm systems, for example using Cloudflare, rate limiting, and WAF rules.
OAuth 2.0 Explained: Authorization, Tokens, Scopes, and Secure Login Without Passwords
OAuth 2.0 enables secure access to third-party APIs and applications without sharing passwords. Discover how the authorization protocol behind every "Sign in with Google" flow works, which grant types exist, and how to implement it securely.
What is Two-Factor Authentication? - Explanation & Meaning
Two-factor authentication adds an extra security layer beyond passwords, for example via authenticator apps, SMS codes, or passkeys for account protection.
Auth0 vs Clerk: Enterprise Auth or Developer-First Identity?
Okta-backed RBAC with 7,000+ integrations or beautiful pre-built React auth components? Auth0 and Clerk target fundamentally different auth needs.