What is Zero Trust? - Explanation & Meaning
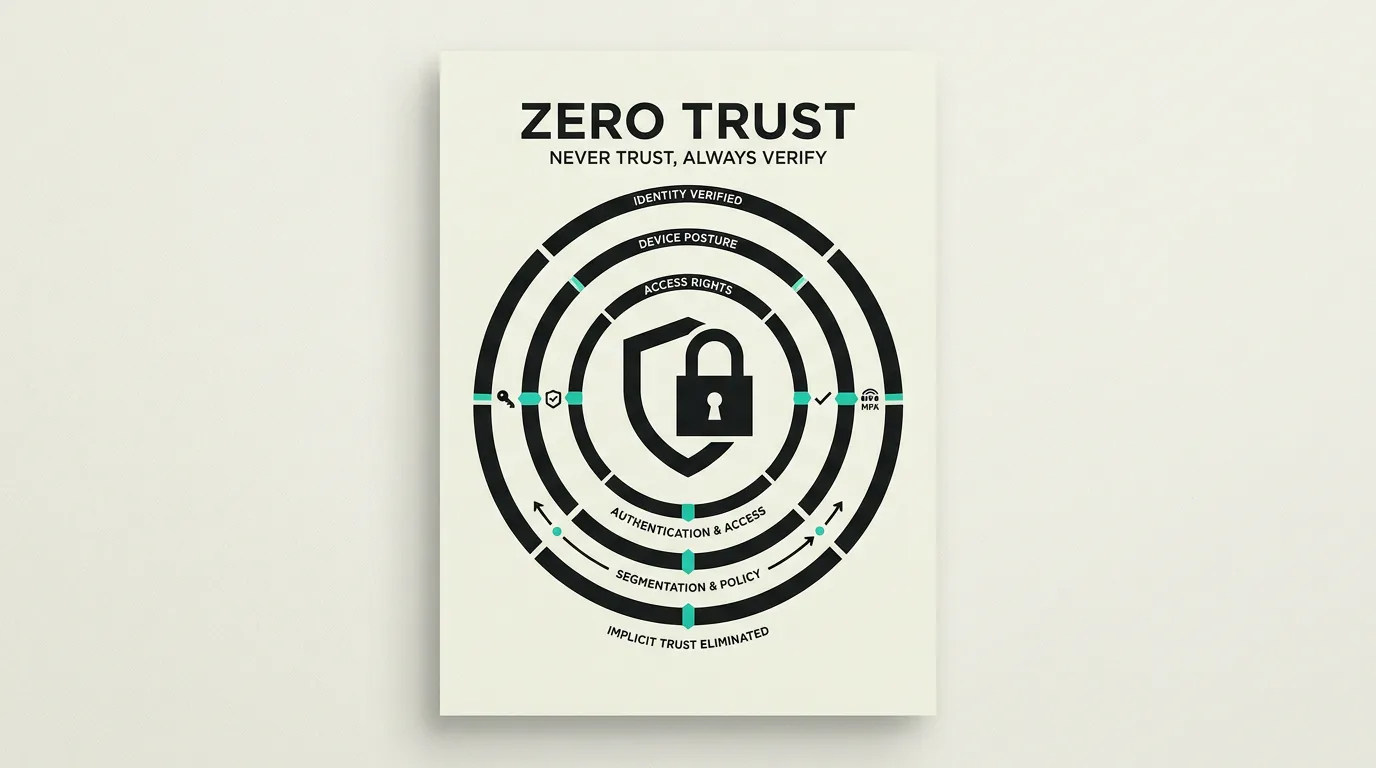
Zero trust never trusts any device or user by default. Every access attempt is verified regardless of location or network position.
Zero trust is a security model based on the principle "never trust, always verify." Unlike traditional models that rely on a secure network perimeter, zero trust treats every access attempt as potentially untrustworthy, regardless of whether it originates from inside or outside the network. The model assumes breaches are inevitable and therefore focuses on limiting damage by explicitly verifying every interaction and granting only the minimum rights necessary for each action.
What is Zero Trust?
Zero trust is a security model based on the principle "never trust, always verify." Unlike traditional models that rely on a secure network perimeter, zero trust treats every access attempt as potentially untrustworthy, regardless of whether it originates from inside or outside the network. The model assumes breaches are inevitable and therefore focuses on limiting damage by explicitly verifying every interaction and granting only the minimum rights necessary for each action.
How does Zero Trust work technically?
Zero-trust architecture (ZTA) eliminates the concept of a trusted internal network. Every user, device, and application must authenticate and authorize with every request based on multiple contextual signals. Microsegmentation divides the network into small, isolated zones, drastically limiting lateral movement by attackers even if they gain an initial foothold. Identity-aware proxies replace traditional VPN connections, granting access based on identity, device posture, and contextual factors such as location and time of day. Software-defined perimeters (SDP) make applications invisible to unauthorized users by minimizing the attack surface. Continuous verification monitors user behavior and dynamically adjusts access rights: a session that starts from a managed device in the expected region can be interrupted if activity suddenly appears from a different country or anomalous API patterns emerge. In 2026, zero trust is no longer an optional framework but a necessity, driven by hybrid work environments, multi-cloud adoption, and increasingly sophisticated threats. NIST SP 800-207 provides guidelines for implementing zero-trust architecture and defines the Policy Decision Point (PDP) and Policy Enforcement Point (PEP) as core components. Multi-factor authentication, least-privilege access, and end-to-end encryption form the pillars of an effective implementation. Device trust verification checks that endpoints meet security baselines such as encrypted storage, current patches, and active endpoint protection before granting access. Conditional access policies in platforms like Azure AD and Okta translate zero-trust principles into configurable rules that automate context-dependent decisions. For API traffic, zero trust means that every service-to-service call is verified with mutual TLS or OAuth 2.0 client credentials, ensuring that even internal communication does not rely on implicit trust. Zero Trust Network Access (ZTNA) replaces VPN solutions by granting application-specific access rather than full network access, drastically shrinking the blast radius in case of compromise. Security Service Edge (SSE) combines ZTNA, Secure Web Gateway, and Cloud Access Security Broker into one platform for unified policy enforcement. Just-in-time (JIT) access grants elevated privileges only when needed and automatically revokes them after a defined period, eliminating the risk of standing privileges. Automated compliance checks continuously validate whether zero-trust configurations adhere to organizational policies and flag configuration drift before it becomes exploitable.
How does MG Software apply Zero Trust in practice?
MG Software applies zero-trust principles in the applications we build. Every API call is authenticated and authorized using short-lived JWT tokens regardless of origin. We implement role-based access control (RBAC) and attribute-based access control (ABAC) with least-privilege principles in our software designs. Supabase Row Level Security forms the database layer of our zero-trust model: even if an API layer is bypassed, the database enforces authorization at the row level. For clients modernizing their infrastructure, we advise on zero-trust strategies ranging from microsegmentation and conditional access to identity-aware access management. We guide the phased migration from legacy networks to a model where every application and endpoint is explicitly verified before data traffic is permitted. We monitor all authorization decisions via structured logging and alerting so anomalous patterns are quickly detected and investigated. Our zero-trust implementations also include device posture checks that verify devices meet security requirements before access is granted.
Why does Zero Trust matter?
Zero trust reduces blast radius after credential theft or device compromise by requiring explicit verification for each access decision. That aligns security with hybrid work, multi-cloud, and SaaS environments where the classic castle-and-moat model increasingly fails. By verifying every access attempt, lateral movement is contained so a breach in one segment does not automatically lead to access to crown jewels. For organizations handling sensitive data, zero trust is also a strong signal to customers, partners, and regulators that security is taken seriously. The investment in identity, segmentation, and monitoring pays back through shorter incident response times and a smaller blast radius when incidents do occur. Cyber insurers factor zero-trust architectures into their risk assessments, which can lead to lower premiums and better coverage terms.
Common mistakes with Zero Trust
Companies rebrand an existing VPN as zero trust without actually implementing strong identity signals, device verification, segmentation, and logging. Other implementations focus only on employee workstations but forget machine-to-machine and API traffic, leaving internal data paths unprotected. Broad admin roles that are never decomposed enable lateral movement and undermine the entire model. Organizations that treat zero trust as a single product rather than an architectural principle become frustrated when a point solution fails to cover all access paths. Finally, teams often forget legacy applications that do not support modern authentication protocols, creating exceptions that punch holes in an otherwise solid implementation. Paying insufficient attention to the user experience of zero-trust flows, causing employees to seek workarounds that undermine security.
What are some examples of Zero Trust?
- A multinational replacing its traditional VPN access with a zero-trust network where employees only access specific applications based on their role, device posture, and location, without ever opening a broad network path.
- A cloud-native organization implementing microsegmentation so a compromised workstation does not automatically have access to sensitive databases, internal services, or other network segments within the same cloud environment.
- A financial firm applying continuous verification that automatically terminates a user session when anomalous behavior is detected, such as unusual login times, location changes, or unrecognized device characteristics.
- A software company implementing mutual TLS between all internal microservices, so that service-to-service communication is always verified and encrypted even within the same Kubernetes cluster.
- A hospital deploying conditional access policies so clinicians can only access the electronic health record from managed devices with current patches and disk encryption, while personal devices have read-only access to schedules.
Related terms
Frequently asked questions
We work with this every day
The same expertise you are reading about, we put to work for clients across Europe.
See what we doRelated articles
Single Sign-On (SSO) Explained: Protocols, Identity Providers and Enterprise Security
Single Sign-On lets users access multiple applications with a single login through an Identity Provider. Learn how SAML 2.0, OAuth 2.0 and OIDC work, which IdP solutions are available, and why SSO is essential for enterprise security and compliance.
Auth0 vs Clerk: Enterprise Auth or Developer-First Identity?
Okta-backed RBAC with 7,000+ integrations or beautiful pre-built React auth components? Auth0 and Clerk target fundamentally different auth needs.
Keycloak vs Auth0: Self-Hosted Identity or Managed Service?
Self-hosted identity management or a fully managed platform? Keycloak offers open-source control while Auth0 delivers speed via Okta's ecosystem.
What Is an API? How Application Programming Interfaces Power Modern Software
APIs enable software applications to communicate through standardized protocols and endpoints, powering everything from payment processing and CRM integrations to real-time data exchange between microservices.