Auth0 vs Clerk: Enterprise Auth or Developer-First Identity?
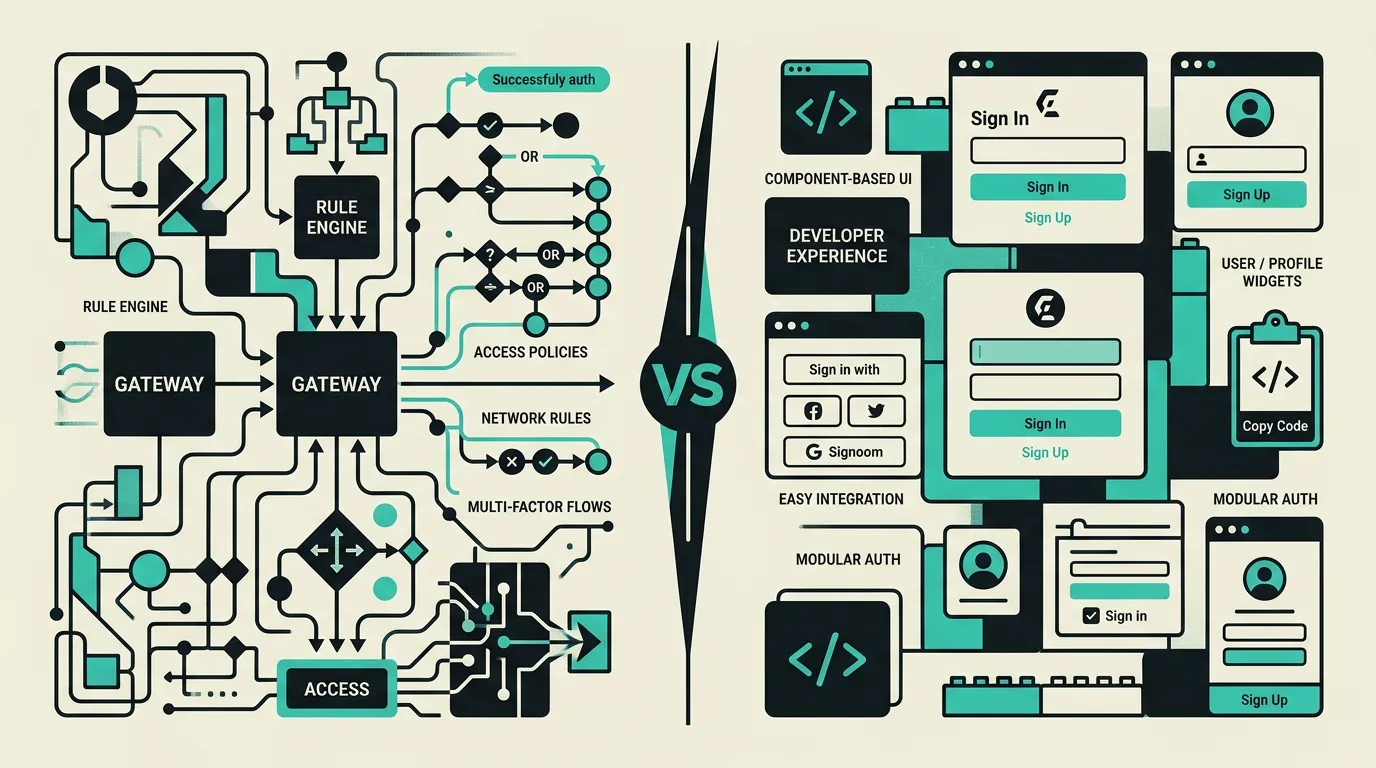
Okta-backed RBAC with 7,000+ integrations or beautiful pre-built React auth components? Auth0 and Clerk target fundamentally different auth needs.
Auth0 and Clerk serve different segments of the authentication market, each with distinct strengths that make them irreplaceable for their target audience. Auth0 is the undisputed choice for enterprise environments where complex authorization with fine-grained permissions, compliance certifications, and a broad integration ecosystem with 7,000+ connections are essential. Clerk has captured a significant portion of the modern web application market with a superior developer experience for React and Next.js. Clerk's pre-built components save weeks of development time and deliver a polished user experience immediately, while Auth0 provides the depth and compliance certifications that enterprise customers in regulated sectors need. Your choice ultimately depends on the complexity of your authorization requirements, your compliance needs, and your technical stack.
Background
Authentication is one of the most critical and simultaneously most underestimated parts of any web application. A wrong choice can lead to security vulnerabilities, poor user experience, or weeks of wasted development time. The choice between an enterprise-grade platform like Auth0 and a developer-focused solution like Clerk determines not only the security of your application, but also the speed at which your team can implement, maintain, and extend authentication. In 2026, we see a clear trend where startups and scale-ups choose Clerk for the developer experience, while enterprises continue to prefer Auth0 for compliance certifications and the broad integration ecosystem.
Auth0
An enterprise-grade authentication and authorization platform owned by Okta, used by more than 18,000 organizations worldwide for securing applications and APIs. Auth0 offers extensive RBAC (Role-Based Access Control), fine-grained permissions, machine-to-machine authentication via client credentials flow, over 7,000 integrations via the Okta ecosystem, and advanced security features like breached password detection, adaptive MFA, bot detection, and attack protection. The platform serves both B2C and B2B use cases with Organizations support for multi-tenant architectures.
Clerk
A modern authentication platform purpose-built for React and Next.js applications that has fundamentally improved the developer experience of authentication. Clerk delivers beautiful, fully styled and customizable UI components for sign-in, sign-up, user management, and organization management. The platform provides an exceptional developer experience with simple SDK integration via npm packages, a user-friendly real-time dashboard, built-in user profile pages, webhook integrations, and support for modern frameworks like Next.js, Remix, Expo, and Astro.
What are the key differences between Auth0 and Clerk?
| Feature | Auth0 | Clerk |
|---|---|---|
| Target audience | Enterprise and large organizations with complex auth and compliance requirements | Startups and modern web applications built with React, Next.js, or other modern frameworks |
| UI components | Universal Login with limited customization, Lock widget, and custom login pages | Full pre-built React components (SignIn, SignUp, UserButton, UserProfile, OrganizationSwitcher) |
| RBAC & authorization | Advanced RBAC with fine-grained permissions, Organizations for B2B multi-tenant | Roles and permissions with Organizations since 2024, growing but less deep than Auth0 |
| Machine-to-machine | Full M2M authentication with client credentials flow and API authorization | Limited M2M support, primary focus on user authentication and session management |
| Integrations | 7,000+ integrations via Okta ecosystem, enterprise SSO, LDAP, and Active Directory | Focus on modern web ecosystem: Next.js, Remix, Expo, Astro with webhooks for custom integrations |
| Pricing | Free up to 25,000 MAU with limited features, then usage-based with enterprise tiers | Free up to 10,000 MAU with more standard features, then $0.02/MAU with Pro plan |
| Developer experience | Extensive documentation and SDKs for 30+ languages, but more complex setup | Superior DX with npm install, copy-paste components, and real-time dashboard preview |
| Compliance | SOC 2 Type II, HIPAA-ready, GDPR-compliant, BAA available, FedRAMP-ready | SOC 2 Type II certified, GDPR-compliant, growing compliance offering |
When to choose which?
Choose Auth0 when...
Choose Auth0 when your organization requires complex authorization rules with fine-grained permissions, manages multiple tenant environments via Organizations, or needs enterprise SSO integrations with existing SAML/OIDC providers and LDAP/Active Directory. Auth0 is also the right choice when machine-to-machine authentication is a core requirement, when you operate in a regulated sector requiring HIPAA BAA or FedRAMP, or when your organization already invests in the Okta ecosystem.
Choose Clerk when...
Choose Clerk when building a modern React or Next.js application where developer experience and speed of integration matter most. Clerk excels when you need beautiful pre-built auth UI components, a managed user dashboard, and want to launch a polished sign-in flow within hours rather than days. Also choose Clerk for SaaS products that need to go to market quickly without investing weeks in custom auth implementation.
What is the verdict on Auth0 vs Clerk?
Auth0 and Clerk serve different segments of the authentication market, each with distinct strengths that make them irreplaceable for their target audience. Auth0 is the undisputed choice for enterprise environments where complex authorization with fine-grained permissions, compliance certifications, and a broad integration ecosystem with 7,000+ connections are essential. Clerk has captured a significant portion of the modern web application market with a superior developer experience for React and Next.js. Clerk's pre-built components save weeks of development time and deliver a polished user experience immediately, while Auth0 provides the depth and compliance certifications that enterprise customers in regulated sectors need. Your choice ultimately depends on the complexity of your authorization requirements, your compliance needs, and your technical stack.
Which option does MG Software recommend?
At MG Software, we use Clerk as our primary authentication solution for new projects built with Next.js. The seamless integration via a simple npm install, the beautiful production-ready UI components, and the user-friendly real-time dashboard make Clerk ideal for the modern web applications we build. We have reduced authentication implementations from weeks to hours thanks to Clerk's developer experience. For enterprise clients with complex B2B multi-tenant requirements, existing Okta integrations, or compliance frameworks like HIPAA, we recommend Auth0. Our experience shows that Clerk significantly reduces time-to-market without compromising on security or user experience.
Migrating: what to consider?
Migrating from Auth0 to Clerk requires exporting user data via the Auth0 Management API and importing into Clerk via their user import tools. Password hashes can be transferred if you use bcrypt in Auth0. Custom RBAC rules built in Auth0 Actions need to be rebuilt using Clerk's permissions system. Social login providers (Google, GitHub, etc.) must be reconfigured. Plan two to four weeks depending on the complexity of your authorization logic and the number of integrated systems.
Frequently asked questions
We build production software with this stack
Our developers work with these tools daily for clients across Europe. Price estimate within 24 hours.
Discuss your project